Introduction
Cybersecurity frameworks are often designed with modern IT infrastructures in mind, but industrial systems rarely operate under the same assumptions. As organizations across Europe prepare for NIS2 compliance, many are discovering that traditional IT security controls do not easily translate to Operational Technology (OT) environments. In industrial environments, implementing cybersecurity measures is not only a technical challenge but often a matter of operational feasibility.
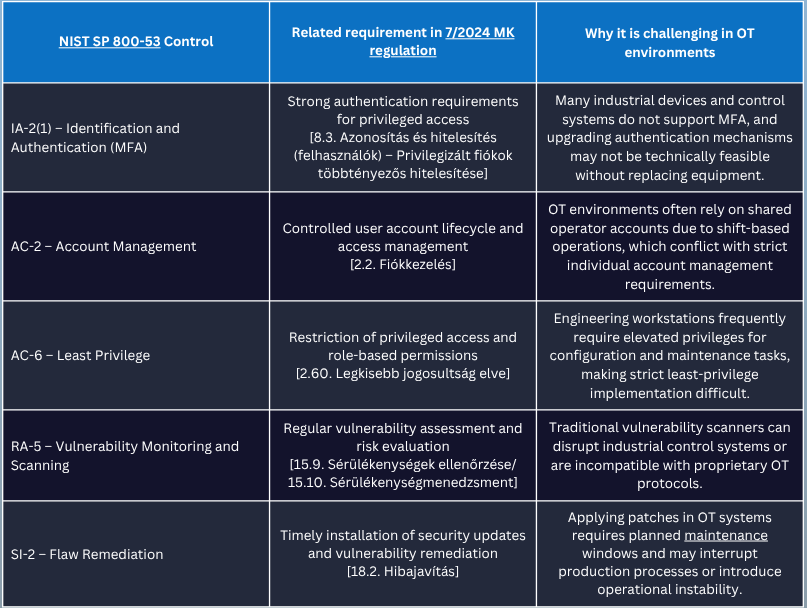
In Hungary, the current regulation relies on control framework derived from NIST SP 800-53, which provide a comprehensive baseline for information security governance. However, this framework was originally designed for traditional IT systems, meaning that their direct application in OT environments can create practical implementation challenges.
Why NIS2 Compliance is Challenging in OT Environments
OT environments are typically designed for long operational lifecycles, with many industrial systems remaining in service for decades and often running software or firmware that is ten to twenty years old. In many cases, vendors no longer provide security updates for these legacy systems, leaving organizations with limited options for addressing newly discovered vulnerabilities, while replacing such infrastructure may require significant investment and disrupt critical operations. At the same time, many OT systems were not designed with modern cybersecurity practices in mind and often lack support for baseline controls commonly used in IT environments, such as multi-factor authentication. Authentication mechanisms may rely on shared accounts or basic password-based access, and logging or monitoring capabilities are frequently limited or entirely absent. Additionally, many industrial devices are incompatible with modern endpoint security solutions, which further complicates the implementation of standardized cybersecurity controls. Frameworks such as NIST SP 800-53 typically rely on technologies and capabilities that are common in enterprise IT infrastructures but less prevalent in OT environments.
Moreover, Identity and Access Management presents unique challenges in industrial systems. The same scenario as before: shared accounts used by multiple personnel during shift-based work. Engineering workstations often require elevated privileges to perform configuration or maintenance tasks, which can increase the potential impact of compromised credentials. In addition, remote access by vendors for maintenance or troubleshooting is common in OT environments, introducing additional risks if access controls are not properly managed.
Patch and vulnerability management also can be particularly complex in industrial systems. Software updates typically require carefully planned maintenance windows to avoid disrupting operational processes. In many cases, patching activities may temporarily interrupt production or critical services, which limits how frequently updates can be applied. Furthermore, applying patches in OT systems may carry the risk of unexpected system instability, making organizations cautious about deploying updates without extensive testing.
Interpretation of Legal and Standard References
The implementation of cybersecurity controls in OT environments often reveals a gap between regulatory expectations and operational realities. The table below illustrates several examples where requirements derived from NIST SP 800-53 and reflected in the Hungarian 7/2024 MK regulation can present practical challenges when applied to industrial systems.
Closing remarks
Achieving NIS2 compliance in OT environments therefore requires more than simply extending existing IT security controls to industrial systems. Organizations must interpret regulatory requirements in a way that reflects the operational realities of industrial infrastructure and the constraints of legacy technologies. A risk-based approach that prioritizes visibility, network segmentation, and controlled access can often provide more practical security improvements than attempting to replicate traditional IT controls in full. At the same time, closer collaboration between IT security teams, OT engineers and compliance professionals is essential to ensure that both security and operational continuity are maintained. As regulatory expectations and industrial digitalization continue to evolve, bridging the gap between compliance frameworks and operational technology environments will remain a key challenge for many organizations.
Relation to Black Cell Services
In our work, we frequently support organizations in translating regulatory requirements into practical and operationally feasible security measures. Our services include NIS2 gap assessment, audit preparation support, and the development of tailored cybersecurity risk management frameworks that take into account the specific characteristics of complex environments. Through these activities, we help organizations better understand their compliance gaps, prioritize remediation efforts, and strengthen their cybersecurity posture while meeting regulatory expectations.
If you have any question or are interested in our services, do not hesitate to contact us via [email protected].
Author
Viktória Hankó
JUNIOR INFORMATION SECURITY COMPLIANCE CONSULTANT
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...