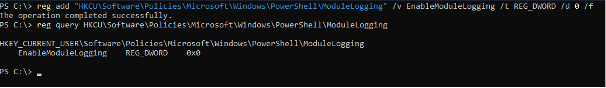
PowerShell Logging Disabled Via Registry Key Tampering
Disabling PowerShell logging is one of the most effective ways to reduce defender visibility during an intrusion. Attackers may inspect registry keys, test execution to see what appears in the event logs, and review group policy settings. Once they understand the existing logging posture, they proceed to disable the relevant controls. Setting registry values, such as EnableModuleLogging, EnableScriptBlockLogging, EnableScriptBlockInvocationLogging, EnableTranscripting, to 0 turns the associated features off.
With a more permissive environment where actions are far less observable, attackers can load in‑memory payloads, invoke .NET assemblies, or operate command‑and‑control toolsets with significantly reduced likelihood of detection. Tools that rely heavily on PowerShell, such as credential harvesting frameworks or Active Directory reconnaissance utilities, also become more effective from the attacker’s perspective because their behavior is no longer exposed through script block event logs. Disabling logging transforms PowerShell from a highly monitored administrative tool into a low‑visibility execution platform that better supports continued malicious activity.
The loss of visibility helps the attacker transition to lateral movement. PowerShell is frequently used to execute remote commands through mechanisms such as WinRM, PSRemoting, and WMI. When logging is disabled, these remote operations avoid generating script‑level telemetry, allowing the attacker to reuse compromised credentials and pivot across hosts with minimal traceability.
The absence of logging also benefits the establishment of persistence mechanisms. Many persistence techniques, such as creating scheduled tasks, modifying autorun registry keys, registering WMI event subscriptions, or configuring recurring PowerShell jobs, are typically executed through PowerShell commands.
Some adversaries even re‑enable logging once their actions are complete, restoring the system to a state that appears normal. This reduces the likelihood that defenders will notice suspicious gaps during routine log reviews.
These registry modifications are quiet, often applied under the user’s own registry hive, and can bypass some traditional monitoring mechanisms. Detailed telemetry shows which commands were executed, actual script contents, parameters, decoded payloads, and contextual metadata. Without logging, these operations become significantly harder to trace. Incident responders face major challenges when reconstructing timelines or understanding attacker behavior.
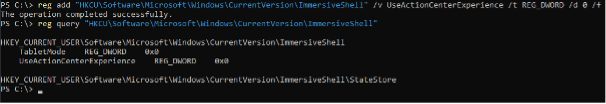
Disable Windows Security Center Notifications
When an attacker disables Windows Security Center notifications by setting the value of UseActionCenterExperience to 0, the suppression prevents the user from seeing visible signs that their system’s defenses have been weakened or disabled. Azorult uses this exact method to evade detection by hiding updates and security notifications, allowing malicious activity to continue without drawing attention.
Disabling the Action Center’s ability to display warnings gives attackers the ability to alter system security settings, such as turning off antivirus protection, stopping the firewall, or blocking updates, without triggering alerts that might prompt user intervention. Because the Action Center is responsible for communicating the system’s security posture, disabling it removes a critical feedback loop between Windows and the user. This enables long‑term persistence, as malicious processes, scheduled tasks, or implants can operate quietly without triggering suspicion.
The abuse of registry‑based notification suppression is not new. Microsoft previously removed older registry keys, such as AntiVirusDisableNotify and FirewallDisableNotify, because attackers were misusing them to hide critical security warnings from users. This historical behavior demonstrates that suppressing notifications through registry edits is a well‑established attacker tactic. The UseActionCenterExperience value represents a modern variant of this same technique, giving adversaries a low‑effort but highly effective method to conceal the security degradation caused by their actions.
Author
Gábor Lázár
L2 SOC ANALYST / ESM ENGINEER
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...