In a network, cables and network devices can break down at any time, and if there is a problem, packets can fail to reach their destination. Therefore, it is necessary to automatically update the routes. The L3 devices obtain routing information from other routers through their interfaces by supporting traffic routing protocols. They populate the best routes in their routing tables and delete route entries that are no longer current. So, routing protocols are used to negotiate and maintain routing tables.
Compared to static routing, dynamic routing protocols are preferable because they save time and effort for network administrators. There is no need to manually configure individual routes and maintenance of routes in case of failure is avoided. This is especially important in larger networks with numerous routes.
RIP (Routing Information Protocol)
The RIPv1 is a well-known distance vector based IGP (Interior Gateway Protocol). Although it’s simple, its convergence can be slow when topology changes. To configure RIP, you need to set the IP addresses of the networks, the route cost (hop count), and timing parameters on the router. Targets can be networks, subnets, or hosts. In the first version, the subnet mask is only available within a network, so it’s not clear whether the destination is a host or a subnet. As a result, the entire network must be advertised. The protocol allows a maximum of 15 hops, 16 is considered infinite. Routers periodically send their tables to a neighboring router at regular intervals (every 30 seconds). There are two other types of timers: expiration and garbage collection. The expiration timer counts down from 180 seconds, and if it fails to update, the neighboring network is considered unavailable. The garbage collector timer then starts counting down from 120 seconds: if the neighbor status does not change, the route entry is removed from the table.
Compared to the first version, more features have been added to RIPv2. It now includes features such as support for Variable Length Subnet Masking (VLSM) and Classless Inter-Domain Routing (CIDR). Since RIP advertises through a UDP port and thus anyone can hijack the traffic, the packets must be authenticated. Authentication can be done with a password or with the more secure MD5 encoding.
OSPF (Open Shortest Path First)
Unlike distance vector-based protocols, all routers know the topology of the entire network, because they are at the root point themselves. When the network starts, the routers send Link State Advertisements (LSAs) to every other router by flooding (multicast addressing). LSAs contain information about the router interfaces and the IP addresses of the links, among other things. Based on this, each router creates a topological database. The Shortest Path First (SPF) protocol determines the shortest path to other networks, resulting in the creation of a tree topology. The routing table is populated with information from this tree.
The OSPF (Open Shortest Path First) is an open version of the SPF protocol. It is resource-intensive, supports VLSM and provides route authentication (plain text or MD5 hash).
BGP (Border Gateway Protocol)
Routing protocols can also be classified according to where they are used:
- IGP (Interior Gateway Protocol) – within an autonomous system,
- EGP (Exterior Gateway Protocol) – for external connections of autonomous systems.
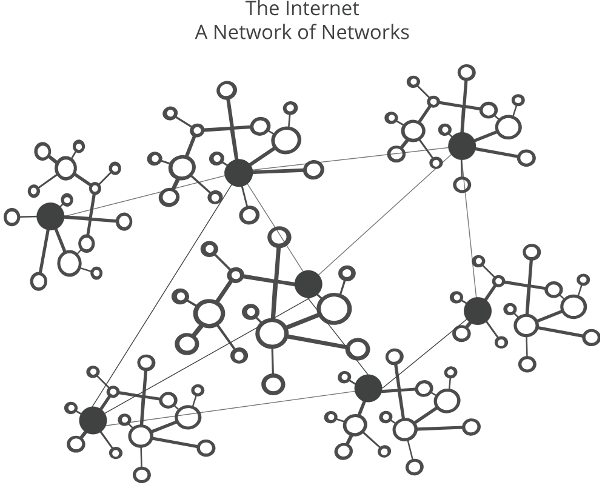
Autonomous system: a network that includes several routers with joint administration. Each autonomous system is managed by an ISP (Internet Service Provider) or organization.
The BGP is EGP and path-vector protocol. Ensures that the route is loop-free. The procedure is to discover advertised routes to the destination. The route to the destination is via autonomous systems, so each route has a list of autonomous systems. The protocol is very memory-intensive because all targets must be in the routing table.
Author

István Szallós
INTEGRATION MANAGER
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...