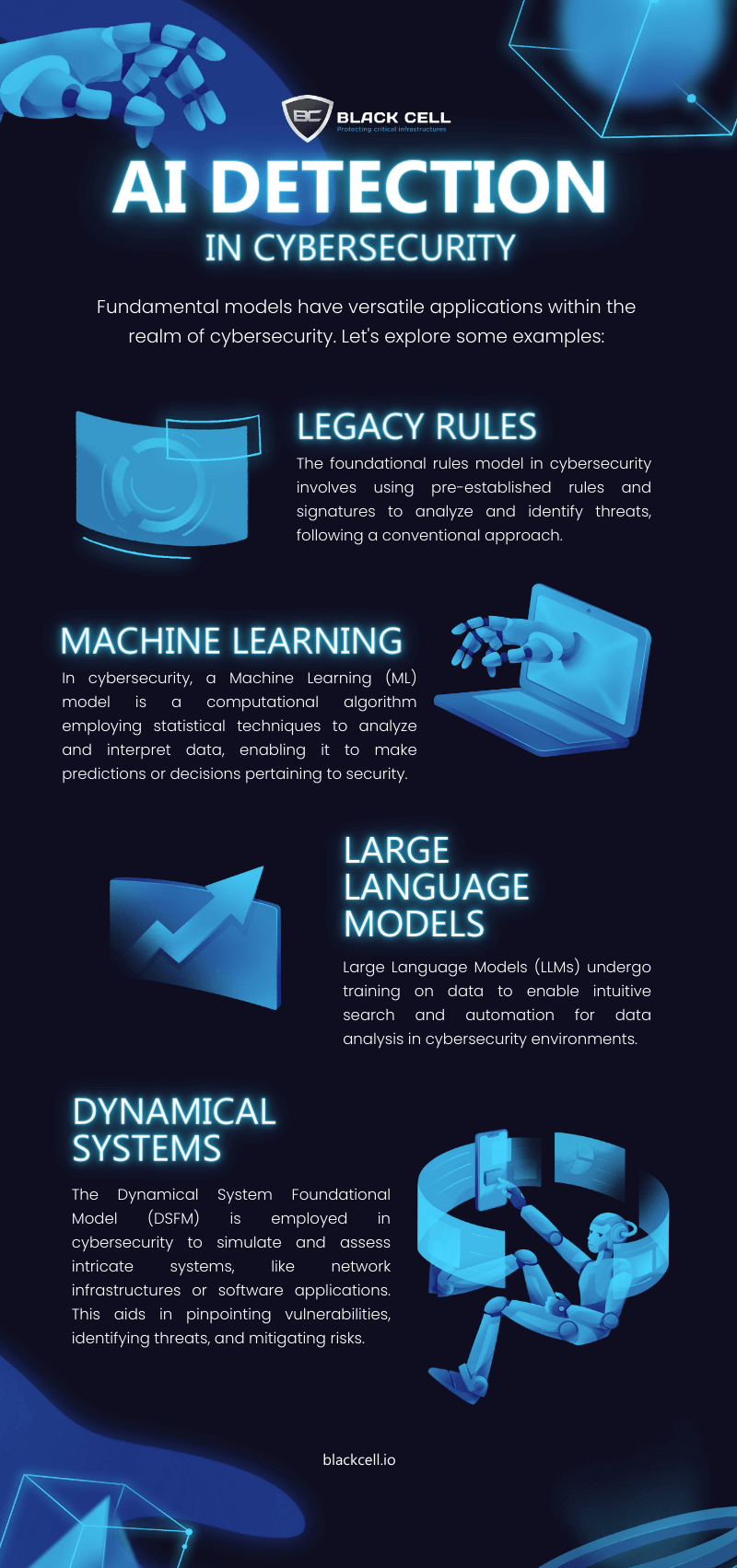
Here are four key approaches:
- Legacy Rules: Traditional rules-based systems set the foundation for cybersecurity, applying predefined criteria to identify threats.
- Machine Learning: By learning from patterns and anomalies, AI adapts to evolving threats, bolstering defenses in real-time.
- Large Language Models: Empowered by extensive training data, these models excel at understanding and contextualizing complex threats.
- Dynamical Systems: Harnessing AI’s ability to adapt and respond dynamically, adding a formidable layer to security measures.
Author

Gergő Gyebnár
CHIEF EXECUTIVE OFFICER
With over a decade of experience in IT security and a background in business development and leadership, he brings valuable expertise to the role. As CEO, Gergő is responsible for leading the expansion of Black Cell’s OT Security and Detection Engineering services worldwide.
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...