In a world where technology evolves at an unprecedented pace, there are few things as exciting as stumbling upon a device that captures the spirit of the past while embracing the possibilities of the future. The Beepy, a compact handheld device developed by SQFMI, does just that. Blending nostalgia with modern innovation, the Beepy invites Linux enthusiasts on a journey of exploration, coding, and customization. In this review, we delve into the hardware, software, and potential of this pocket-sized Linux hacking playground.
A Walk Down Memory Lane
The Beepy invokes memories of a time when modems sang, and Linux was a realm of adventure. The journey to taming this operating system was not for the faint of heart, as each kernel update unlocked new possibilities. The Beepy nods to those early days when technology was a playground for the curious and the bold.
Unveiling the Hardware
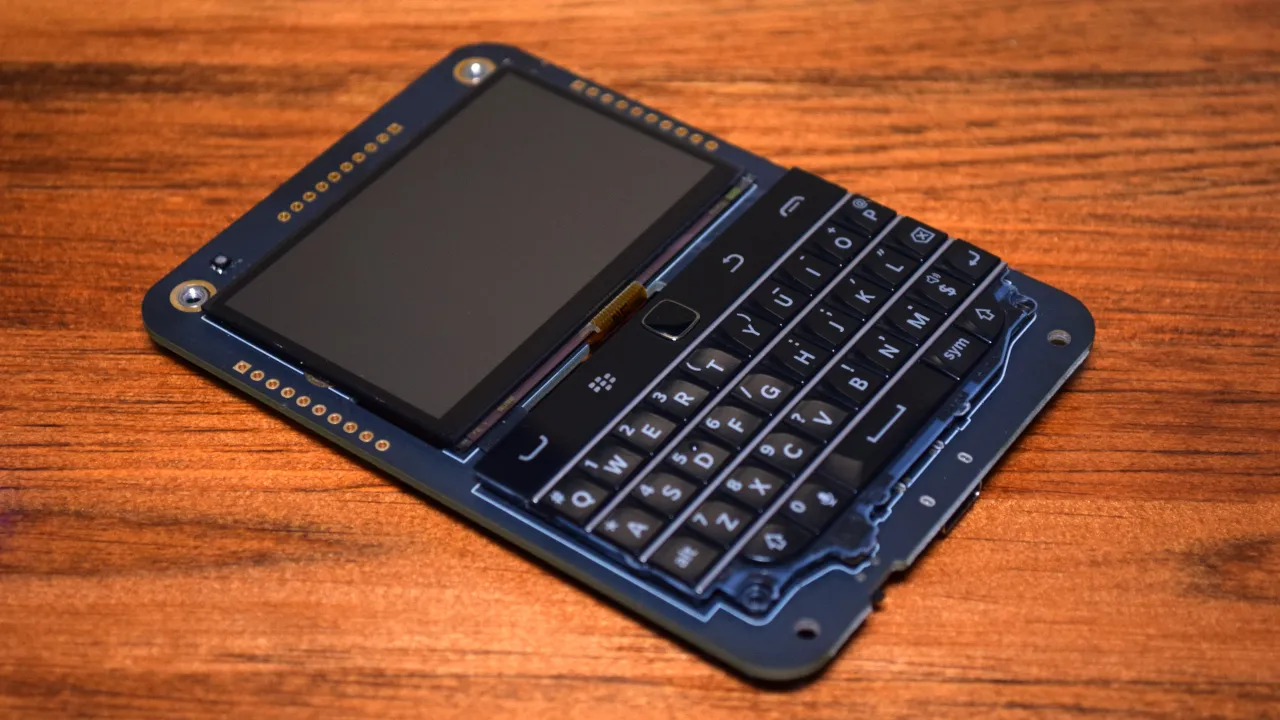
At its core, the Beepy is a fusion of nostalgic design and contemporary components. It features a BlackBerry keyboard, a 400 x 200 Sharp Memory LCD, and a rechargeable battery. However, it’s important to note that the Beepy is not a standalone computer; it’s designed to host a Raspberry Pi Zero, with the option of purchasing it pre-installed with a Pi Zero 2. The clever arrangement of flexible pins connects the Raspberry Pi to the Beepy, making it easy to swap or upgrade the core component without the need for soldering.
The keyboard, a genuine BlackBerry board, harkens back to the days of tactile input. The satisfying feel of the keys and the inclusion of necessary symbols and punctuation marks make it a joy for those who appreciate the beauty of physical keyboards.
The Beepy’s most unique feature is its Sharp Memory LCD, offering high contrast and daylight readability while consuming minimal power. Although it lacks graphical capabilities, its potential for text-based applications is promising. However, the limited resolution of 400 x 240 may pose challenges for adapting certain programs.
Software Adventures
For Linux enthusiasts and hardware hackers, the Beepy’s allure lies in its potential for experimentation and customization. While the device comes with a script for installing necessary kernel drivers, it’s essential to note that the Beepy doesn’t offer an out-of-the-box consumer experience. Rather, it encourages users to dive into the world of terminal-based programs and coding.
The provided drivers for the keyboard and display work well, showcasing the device’s capabilities. However, limitations arise when trying to use the HDMI port while the Memory LCD driver is active, emphasizing the Beepy’s focus on terminal-based interactions.
Documentation and support, primarily found in the project’s Discord and Matrix servers, remain in flux. While this community-driven approach fosters collaboration and innovation, more structured and easily accessible documentation is needed to accommodate a broader user base.
Battery Life and Power Management
The Beepy’s battery life varies based on usage scenarios. For light tasks, such as browsing a terminal, the device can last up to eight hours. However, more power-intensive activities, such as running WiFi adapters or external devices, significantly reduce battery life. The Beepy’s power management, while functional, has room for improvement, with potential concerns over the charging circuit’s long recharge times and certain components’ failure rates.
Final Thoughts
The Beepy is a glimpse into a world of possibilities where Linux hacking and tinkering reign supreme. It bridges the gap between nostalgia and innovation, inviting users to relive the thrill of exploration while embracing the power of modern technology. The hardware’s affordable price point makes it an appealing canvas for hackers, tinkerers, and Linux enthusiasts to create, experiment, and embark on new coding adventures. As the Beepy community grows and documentation improves, this pocket-sized Linux hacking playground has the potential to inspire a new generation of hackers eager to dive into the world of Linux customization and exploration.
Source: Hackaday
Author

Gergő Gyebnár
CHIEF EXECUTIVE OFFICER
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...




