While it might seem like company databases are filled with mundane files, hackers know the harsh reality. According to Verizon’s Data Breach Investigations Report, the culprits behind cyber attacks come from various corners – outsiders, insiders, company partners, organized crime groups, and affiliated parties.
Here’s a closer look at the percentages for each category:
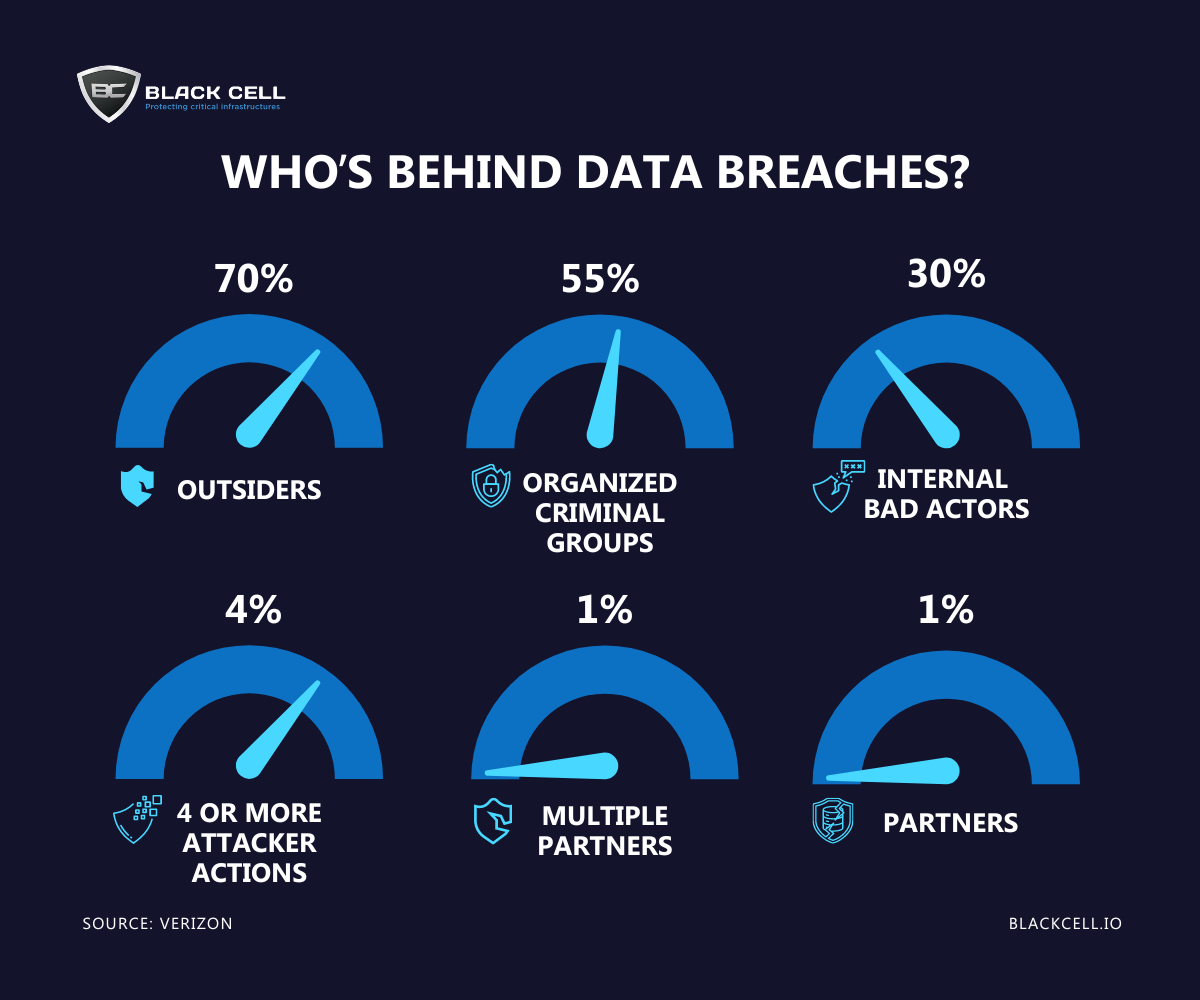
Source: Embroker, Verizon
Author

Péter Szöllősi
OFFENSIVE SECURITY MANAGER
Peter has been the Head of Offensive Security at Black Cell for five years, where he manages the pentester team responsible for providing high-quality ethical hacking services to clients to enhance their security posture. He also contributes to the maintenance and improvement of Black Cell’s security posture with internal and external audits.
Related Posts
Top 4 Cyber Threats Security Leaders Feel Least Prepared For
Even the most experienced security leaders admit they’re not fully ready for every threat lurking...
Global Growth of Cybercrime
In today’s hyper-connected world, cybercrime is no longer a distant threat - it’s a looming...